Key Takeaways
- Combine no-logs VPNs, Tor, privacy operating systems like GrapheneOS, Tails, or Qubes, and encrypted apps to reach roughly 95% digital invisibility against AI fingerprinting and surveillance.
- Match your setup to your threat model and pick secure hardware: Pixel phones for GrapheneOS, USB drives for Tails, and high-RAM laptops for Qubes VM isolation.
- Harden your stack with privacy extensions, metadata purging via ExifTool, full-disk encryption, and device fingerprint evasion through MAC randomization.
- Set up anonymous monetization with Monero, burner accounts, and regular tests on ipleak.net while keeping strict operational security habits.
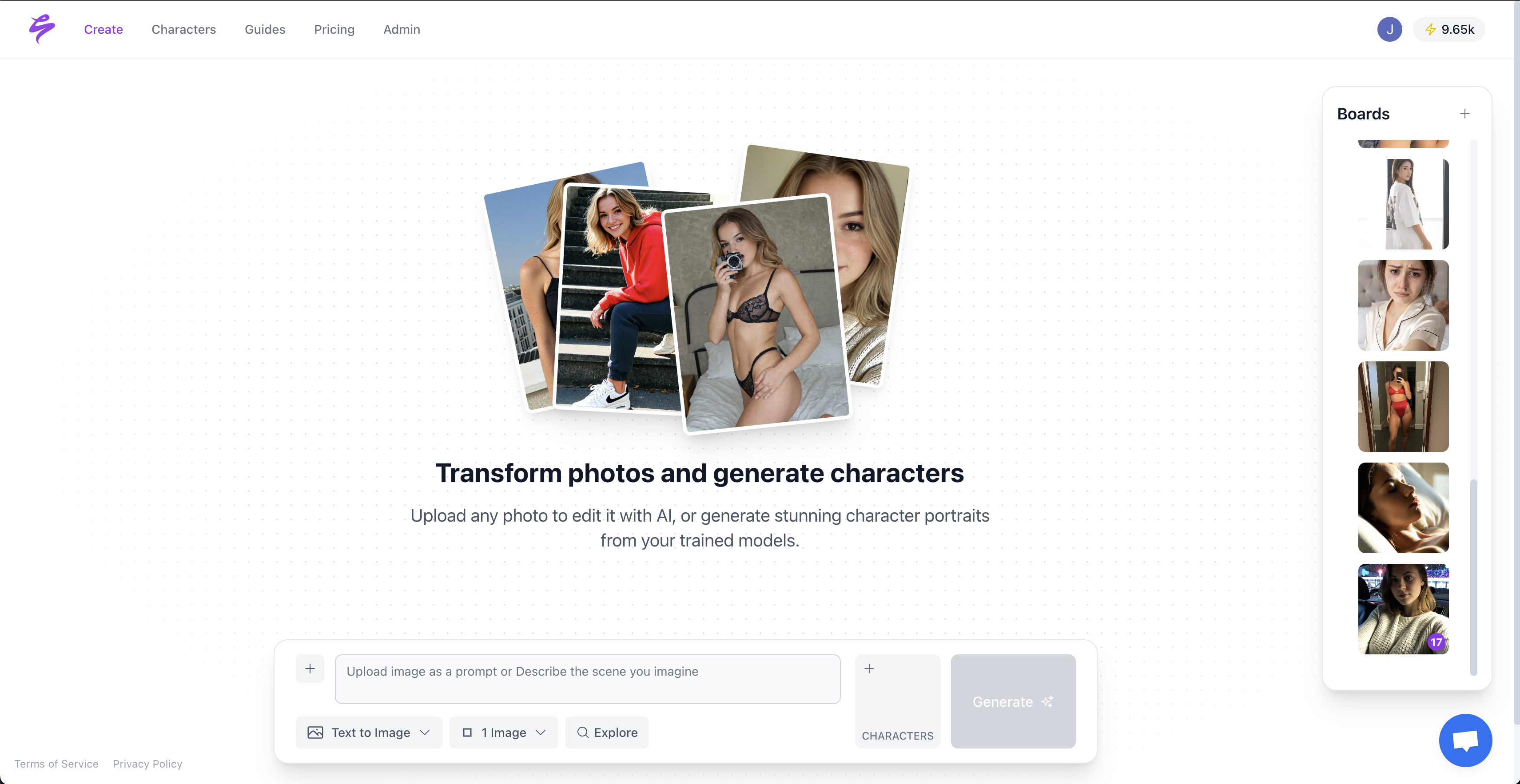
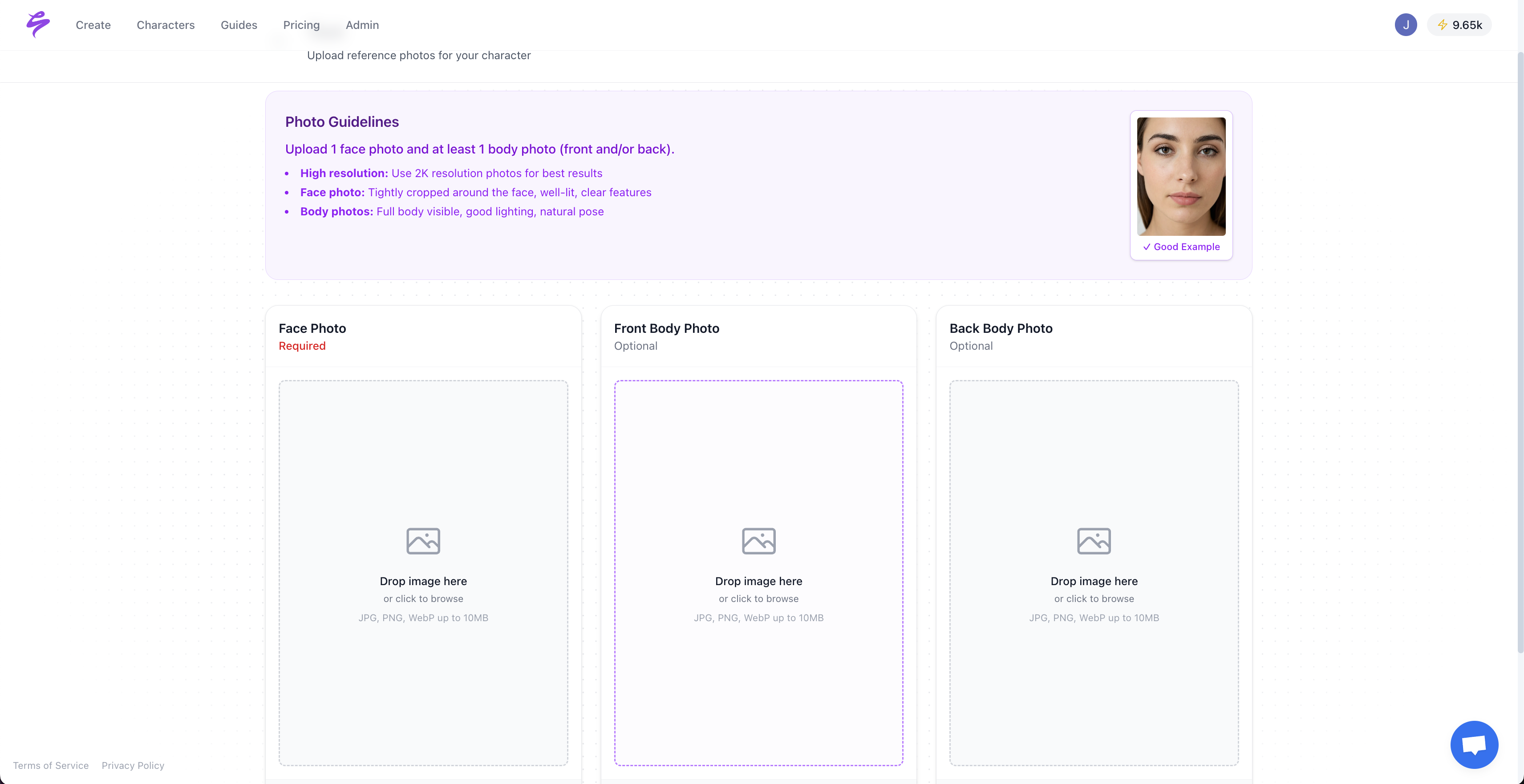
- Scale content creation safely with Sozee.ai metadata-free AI likeness models built from just 3 photos, so you avoid real photoshoots.
12-Step Blueprint for Anonymous Creators in 2026
1. Assess Your Threat Model
Start by defining who you need to stay anonymous from and how they might track you. Browser fingerprinting now relies on standardized identification toolkits that read your OS, browser, fonts, timezone, and GPU signatures. AI-enhanced tracking tools capture richer interactions from website analytics and chat features. For monetized creators, doxxing risks often come from IP leaks during uploads, metadata in exported files, and device fingerprints that connect anonymous accounts to real identities.
2. Choose Secure Hardware
Pick devices that work smoothly with privacy-focused operating systems. Google Pixel phones support GrapheneOS with VPN leak fixes and removed unique device identifiers. For desktop anonymity, most modern laptops can run Tails or Qubes without major issues.
| Device | Best OS | Pros | Cons |
|---|---|---|---|
| Google Pixel | GrapheneOS | Hardware security, MAC randomization | Limited device selection |
| USB Drive (16GB+) | Tails | Universal compatibility, amnesic | Slower performance |
| High-RAM Laptop | Qubes | VM isolation, multi-identity | Resource intensive |
3. Install Privacy-Focused Operating Systems
Run your anonymous work from systems built for privacy instead of general use. Tails OS runs from USB or DVD with preconfigured Tor routing and an amnesic design that wipes data on shutdown. Qubes OS uses virtualization to isolate tasks into separate virtual machines, which works well for managing multiple creator identities. GrapheneOS offers desktop-mode security similar to Qubes for casual browsing when you need mobile flexibility.
4. Chain VPN and Tor for Stronger Protection
Route your traffic through both a trusted VPN and Tor to reduce single points of failure. Tor uses multi-layered encryption with perfect forward secrecy, which makes user identity very hard to trace. Combine Tor with audited no-logs VPNs. ProtonVPN denied all 59 legally binding data requests in 2025, and Windscribe proved its no-logs claims in court. At the same time, about 90% of VPN servers sit on upstream networks that collect NetFlow data, so VPN and Tor chaining becomes critical for serious anonymity.
5. Harden Your Browser Configuration
Turn your browser into a smaller target instead of leaving default settings in place. Install uBlock Origin and CanvasBlocker extensions to cut tracking scripts and canvas fingerprinting. Avoid over-masking by choosing coherent presets where fingerprint signals align realistically. Overly sterile or unique environments can trigger antifraud systems and draw extra attention.
6. Secure Your Communications
Separate your anonymous conversations from your real-life chats on both devices and accounts. Use Signal for messaging and ProtonMail for email, and run them inside isolated Qubes VMs or through Tails sessions. Keep anonymous and real-identity communications off the same device and never share sessions between them.
7. Encrypt All Storage and Sensitive Files
Protect your data at rest so a seized or lost device does not expose your identity. Turn on full-disk encryption with LUKS on Linux systems or use VeraCrypt when you need cross-platform compatibility. Encrypt persistent storage on Tails installations and store sensitive files inside encrypted containers instead of open folders.
8. Strip Metadata from Every Upload
Clean your content of hidden data before it ever reaches a platform. Remove metadata before uploads using ExifTool to strip EXIF data, location information, and other metadata from photos. For videos, rely on client-side tools that remove GPS, timestamps, and device information. AI Metadata Masker removes “Generated by AI” signatures from Sozee-generated content. This step matters because metadata can reveal device models, creation timestamps, and GPS coordinates that connect anonymous uploads to your real-world identity.
9. Build an Anonymous Monetization Stack
Design your payment flows so they never touch your real banking footprint. Use Monero wallets for cryptocurrency transactions and burner payment methods for platforms that require cards. Create separate email addresses and phone numbers for each monetization platform. Keep anonymous creator accounts fully detached from personal bank accounts and legal names.
10. Reduce Device Fingerprinting Signals
Limit how easily platforms can recognize your devices across sessions. GrapheneOS uses MAC address randomization to block long-term device tracking on networks. Use conservative proxy rotation at the end of each session instead of constant changes to build trust. Stable but private patterns often look more human than rapid, erratic switching.
11. Test and Audit Your Anonymity Setup
Regular testing helps you catch leaks before an adversary does. Check your configuration on ipleak.net to look for DNS, WebRTC, and IP leaks. Run browser fingerprinting tests and confirm that all traffic routes through Tor when required. Document your operational security procedures so you can repeat safe workflows and avoid risky improvisation.
12. Maintain Long-Term Operational Security
Consistent habits keep you anonymous more effectively than any single tool. Use burner devices for anonymous work, perform regular data wipes, and avoid breaking character between anonymous and real identities. Scale content production with Sozee.ai to generate unlimited anonymous content from just 3 photos, which removes the need for risky real-world photoshoots. Start creating metadata-free likeness models today and keep your real image offline.
Layered Anonymity: Why 95% Protection Is Realistic
Perfect anonymity does not exist, but tiered defenses can still give you strong protection in practice. High-profile deanonymization cases like Silk Road relied on blockchain analysis, not weaknesses in Tor itself. State-level adversaries usually need significant resources and time to run traffic correlation attacks, which most creators will never face directly.
| Tier | Stack | Effectiveness | Creator Fit |
|---|---|---|---|
| Tier 1 | VPN Only | 60% | Casual privacy |
| Tier 2 | VPN + Tor | 80% | Basic anonymity |
| Tier 3 | Qubes + VPN + Tor + Sozee | 95% | Dedicated anonymous creators |
Advanced Growth and Monetization for Anonymous Creators
Turn your anonymous presence into a scalable business without exposing your identity. Implement cryptocurrency pay-per-view systems and build themed content bundles using Sozee style consistency features. Use Qubes VMs to isolate Sozee.ai sessions and keep SFW and NSFW content fully separated. Generate SFW and NSFW content sets that look convincingly real for OnlyFans, TikTok, and other platforms while your real image stays private.
For anonymous creators, Sozee.ai offers 3-photo instant models with strong privacy by design. Multiply your output 10x with Sozee.ai and start creating now without stepping in front of a camera.
FAQ
Can anyone be completely anonymous on the internet?
Complete anonymity on the internet remains out of reach, even with advanced tools. Combining privacy operating systems like Tails or Qubes with VPN and Tor chains can still reach roughly 95% digital invisibility for most real-world threats. Layered defenses work better than any single tool. For content creators, pairing secure devices with Sozee.ai removes the need for risky real-world photoshoots while keeping anonymity intact through AI-generated content.
Which operating system works best for anonymous creators?
Qubes OS offers the strongest security for creators who juggle multiple identities. It uses VM isolation so you can separate different personas and activities into distinct compartments. Tails delivers excellent portability and amnesia features for temporary anonymous sessions on almost any computer. GrapheneOS supports mobile anonymity with hardened hardware-backed security. Your choice depends on workflow: Qubes for multi-identity management, Tails for portable anonymity, and GrapheneOS for secure mobile use.
Does a VPN alone give enough anonymity?
A VPN alone rarely provides enough anonymity against determined trackers. Modern tracking stacks use device fingerprinting, traffic analysis, and metadata correlation that can bypass simple VPN protection. Effective anonymity usually requires chaining VPNs with Tor, running privacy-focused operating systems, and following strict operational security practices. This combination creates multiple failure points that significantly raise the effort required to deanonymize you.
How can I reduce my existing digital footprint?
Completely erasing a digital footprint is not realistic, but you can shrink it and prevent new traces. Use ExifTool for images and specialized video metadata cleaners to remove location data, device identifiers, and creation timestamps from all content before upload. For ongoing anonymity, rely on Sozee.ai metadata-free exports instead of producing new traceable real-world content. Over time, your visible activity shifts toward anonymized assets instead of personal media.
Can GrapheneOS support truly anonymous browsing?
GrapheneOS significantly improves mobile anonymity compared with standard Android builds. It adds MAC address randomization, removes Google tracking components, and hardens core system elements. True anonymity still depends on how you use the device. Combine GrapheneOS with VPN and Tor chains and follow careful operational security to avoid identity leaks. The OS provides a strong privacy foundation, but configuration and daily habits ultimately decide your anonymity level.
