Key Takeaways for Securing AI Social Media Tools
- OAuth 2.1 with PKCE and OIDC is the current standard for AI social media tools, with granular scopes and short-lived tokens that protect high-volume posting.
- Passkeys (FIDO2/WebAuthn) use biometrics and cryptographic checks to block phishing, which keeps creator dashboards safe from AI spoofing.
- Just-in-Time (JIT) authentication issues short-lived credentials for fast onboarding and smaller attack surfaces in dynamic AI content workflows.
- C2PA embeds tamper-evident metadata into media, which proves human oversight and provenance for AI-generated social posts.
- JWT with secure vaulting supports agencies that manage many creator accounts at once; see how Sozee secures multi-creator AI workflows.
Top 5 Authentication Protocols for AI Social Media Content Tools in 2026
1. OAuth 2.1 with PKCE + OIDC for Social Platform Access
OAuth 2.1 with Proof Key for Code Exchange (PKCE) and OpenID Connect (OIDC) is the leading choice for AI social media tools that handle thousands of posts per day. The protocol supports granular scopes such as “write_post”, “manage_media”, and “schedule_content”, which gives precise control over what AI workflows can do. Short-lived access tokens that last 5 to 15 minutes, combined with refresh token rotation, create a strong defense against credential stuffing attacks that target creator tools.
The 2026 implementation stack pairs OAuth 2.1’s mandatory PKCE with identity providers like Stytch or Auth0, which manage token lifecycles automatically. This setup simplifies posting to a single authenticated API call, for example: curl -H "Authorization: Bearer ${SHORT_TOKEN}" -X POST https://graph.instagram.com/v18.0/me/media. This streamlined flow delivers enterprise-grade security, broad social platform compatibility, and permission flows that work well for agencies. The tradeoff is higher initial setup effort and ongoing token management overhead for posting volumes above 1000 posts per hour.
2. Passkeys (FIDO2/WebAuthn) for Creator Dashboard Login
Phishing-resistant authenticators like WebAuthn grew 63% to reach 14% adoption in 2025, which makes passkeys a core layer for AI content dashboard security. These cryptographic credentials resist AI spoofing by verifying both the person through biometrics and the service through cryptographic trust. Passkeys remove password-based risks while keeping sign-in smooth for creators who use AI generation interfaces daily.
Modern deployments pair device biometrics such as fingerprint or Face ID with FIDO2 hardware keys to create multi-modal protection. When you connect passkeys with existing OAuth flows, you get layered security: passkeys secure access to the dashboard, and OAuth tokens secure API posting to social platforms. This combination delivers near-zero phishing risk, a smoother login experience, and strong support for mobile-first creator workflows. The main drawbacks are reliance on supported devices and weaker coverage on older hardware that some creators still use.
3. Just-in-Time (JIT) Authentication Flows for Fast Onboarding
JIT authentication removes the onboarding friction that often kills conversion for AI social media tools. JIT access issues time-bound credentials that exist only during the approved window and then disable automatically. This pattern supports instant creator account provisioning with scopes such as “posts:write”, “analytics:read”, and “audience:manage”, without storing long-term credentials.
Current JIT systems rely on policy engines that grant ephemeral tokens based on real-time risk signals. For AI content tools, this means a creator can connect Instagram or TikTok, generate content, and then lose access automatically once the session ends. The flow inserts MFA at key privilege elevation moments while keeping the overall experience smooth. These choices reduce the attack surface, simplify user lifecycle management, and create audit trails that satisfy compliance teams. The tradeoffs are more complex policy design and possible latency when traffic spikes.
4. C2PA for Authenticating AI-Generated Social Content
Content Provenance and Authenticity (C2PA) solves the problem of proving that AI-generated posts are real, approved, and traceable. C2PA Content Credentials embed authenticity metadata that records creator identity, creation time, and edits in a tamper-evident format. This capability becomes crucial as platforms tighten rules around transparency for AI-generated media.
C2PA works well with OAuth-based posting to create a full authenticity chain. OAuth tokens confirm that a trusted tool posted the content, and C2PA metadata proves where the content came from and who approved it. The Library of Congress C2PA Initiative shows how this can work in real deployments. AI social media tools can attach C2PA signatures during generation, which gives platforms and brands verifiable proof of human oversight. Benefits include easier regulatory compliance, alignment with platform policies, and stronger creator authenticity signals. Costs include extra metadata overhead, uneven platform support, and privacy concerns for creators who prefer anonymity.
5. JWT with Secure Vaulting for Multi-Creator Agencies
JSON Web Tokens (JWT) combined with secure credential vaulting help agencies manage many creator accounts without losing control of security. This pattern stores sensitive social credentials in encrypted vaults such as HashiCorp Vault or AWS Secrets Manager, while JWTs handle sessions and API access. Frequent token rotation, typically every 5 to 15 minutes, limits the value of any stolen token while still supporting heavy posting schedules.
In this model, a vault-backed service issues JWTs that carry claims such as “creator_id”, “platform_scopes”, and “posting_limits”. Agencies can then work with hundreds of creator accounts from a single interface while keeping each set of credentials isolated in the vault. This structure fits AI content tools that serve many OnlyFans or Instagram creators at once. Explore Sozee’s vault-backed, agency-grade authentication to see this pattern in action. Pros include strong multi-account scalability, centralized control, and clear audit trails. Cons include the complexity of running vault infrastructure and the need to design around potential single points of failure.
Recommended Authentication Stack for Creator Economy Platforms
A production-ready authentication stack for AI social media tools should balance setup effort, security coverage, and creator experience. The main tradeoff when choosing protocols is setup complexity versus security scope. Enterprise-scale options such as OAuth 2.1 cover all major platforms but take longer to deploy, while focused tools like passkeys roll out faster but cover narrower use cases. The following comparison table maps each protocol to its strongest deployment scenario.
| Protocol | Social Platforms | Setup Time | Best For |
|---|---|---|---|
| OAuth 2.1 + OIDC | All major platforms | 2-4 weeks | Enterprise scale |
| Passkeys | Dashboard access | 1-2 weeks | User authentication |
| JIT Flows | Platform-agnostic | 3-5 weeks | Dynamic access |
| C2PA | Emerging support | 4-6 weeks | Content authenticity |
The recommended architecture follows a clear sequence: Frontend passkeys for login, OIDC identity provider for user identity, OAuth 2.1 scopes for platform permissions, secure vault for credentials, and finally social media API posting. Best practices start with granular scopes per platform, which limit damage if any token leaks. Short rotation windows, such as 5-minute tokens, further shrink exposure time for attackers. Human-in-the-loop approval for sensitive content adds a manual check that automated systems cannot match for reputational risk. These layers together reflect zero-trust principles, where every API interaction is verified instead of assumed safe.
A simple multi-platform posting flow might look like this: const token = await vault.getToken(creatorId, platform); await postContent(token, aiGeneratedMedia, c2paMetadata);. This pattern keeps each creator’s credentials isolated in the vault while still allowing smooth AI content distribution across platforms. Implement this multi-creator authentication pattern with Sozee’s scalable infrastructure.
Why Sozee.ai Excels at Secure AI Content Authentication
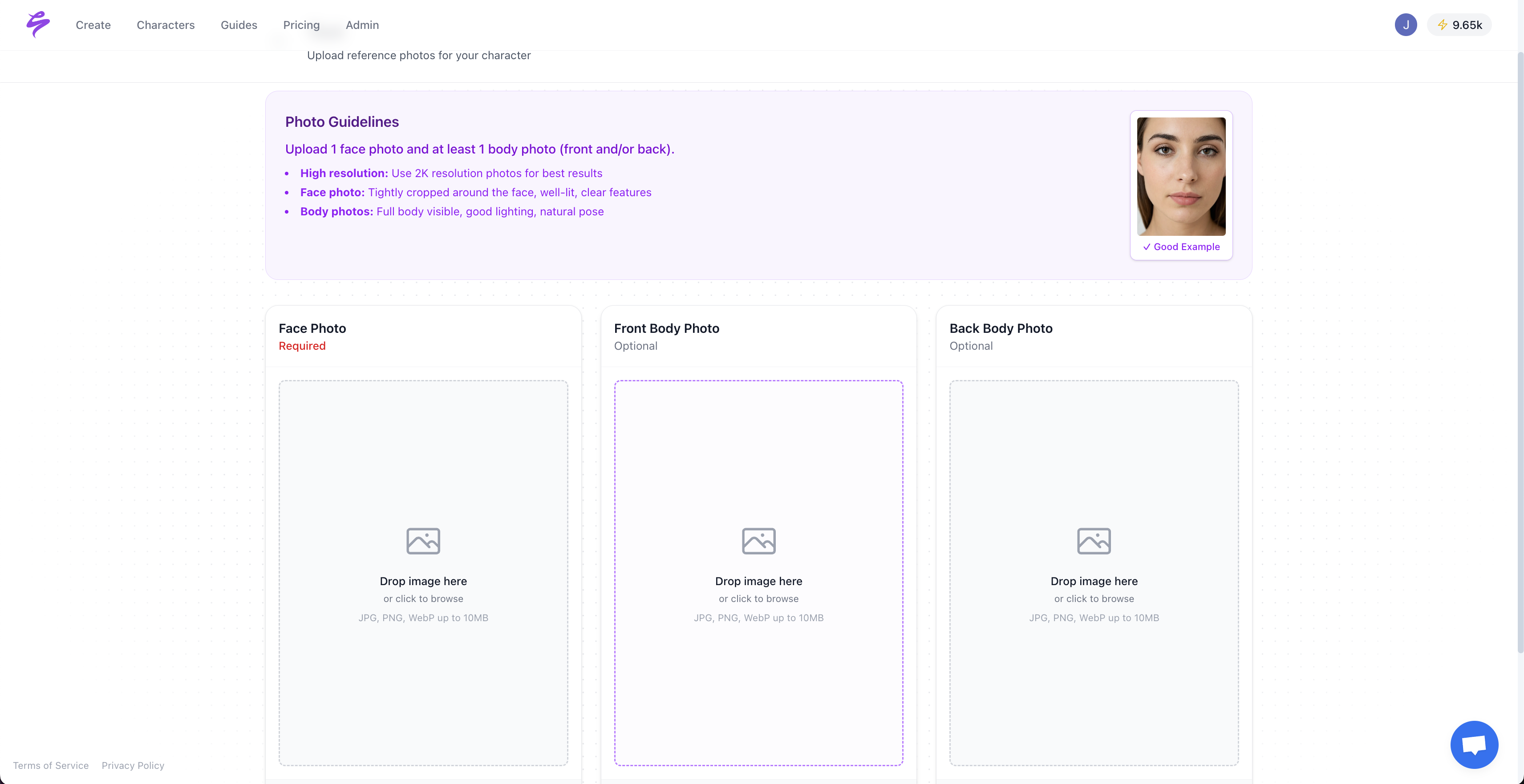
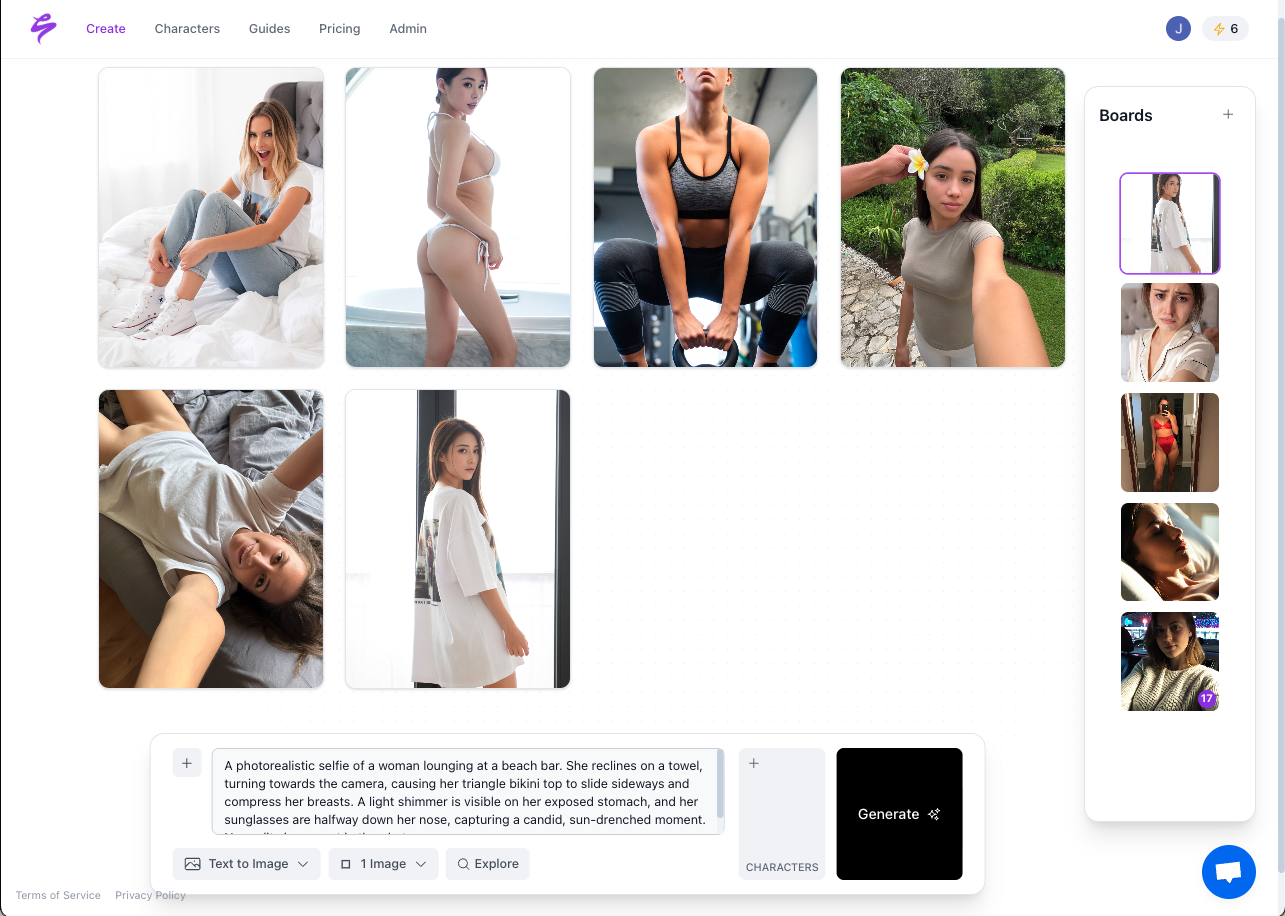
Sozee.ai is an AI Content Studio built for the Creator Economy, with private likeness model creation from just three photos, hyper-realistic content generation, and safe export to OnlyFans, Instagram, TikTok, and more. The platform supports agency approval workflows and protects creator privacy through isolated, private models that never train other systems. Sozee’s architecture supports infinite AI content creation while maintaining realism, security, and strict control over where content goes. Get started with Sozee’s secure AI content studio for creators and agencies.
FAQ
What makes OAuth 2.1 with PKCE mandatory for AI social media tools in 2026?
OAuth 2.1 with PKCE becomes mandatory because regulators and platforms now require stronger proof that tokens come from legitimate flows. As detailed earlier, PKCE’s code verifier mechanism blocks authorization code interception, which is especially risky when AI tools post at scale. In 2026, frameworks require cryptographic evidence that access tokens originated from valid authorization steps, not stolen codes, and PKCE is the widely supported extension that meets this bar. This protection is crucial for tools that manage many creator accounts and sensitive content such as OnlyFans posts or brand campaigns.
Which authentication protocol works best for OnlyFans and adult content posting?
OAuth 2.1 with granular scopes works best for adult content platforms such as OnlyFans. Scoped permissions like “content:upload”, “messages:send”, and “earnings:view” limit what AI tools can do on each account. Short-lived tokens reduce exposure if a token leaks, and secure credential vaulting keeps long-term secrets out of application code. Together, these choices let AI tools handle sensitive adult content while protecting creator privacy and meeting platform rules.
How does C2PA content provenance work with existing authentication protocols?
C2PA acts as a provenance layer on top of existing authentication protocols such as OAuth 2.1. OAuth controls who can post and which APIs they can call, while C2PA adds tamper-evident metadata that proves authenticity and human review. OAuth-authenticated AI tools generate C2PA signatures during content creation, which creates a chain of custody from generation through approval to final posting. This combined approach satisfies security expectations and new transparency rules for AI-generated content.
Are passkeys ready for production use in AI social media applications?
Passkeys based on FIDO2 and WebAuthn are ready for production in 2026 AI social media applications. Apple, Google, and Microsoft support passkeys across major platforms, and providers such as Okta and Auth0 offer enterprise integrations. As mentioned earlier, the phishing-resistant design of passkeys is especially valuable for AI dashboards where creators manage sensitive tools and accounts. The technology works across mobile and desktop, which fits creator workflows that move between devices.
What is the difference between JIT authentication and traditional OAuth flows?
Just-in-Time authentication issues short-lived access that expires automatically after use, while traditional OAuth flows rely on longer-lived tokens and refresh tokens. JIT fits AI social media tools because it supports instant onboarding without storing permanent credentials. When a creator connects an Instagram account, JIT can grant temporary posting access for that session and then revoke it. This pattern reduces the attack surface compared with standard OAuth setups that keep long-lived refresh tokens, which makes it a strong fit for high-volume tools that serve thousands of creators.
