Key Takeaways
- Deepfake fraud has surged to 8 million files by 2025, costing enterprises up to $680,000 per incident and demanding robust digital identity management in text-to-image AI.
- Enterprises rely on 5 core strategies: IAM/RBAC integration, liveness detection, C2PA watermarking, private model isolation, and audit trails to secure AI workflows.
- A 6-step implementation guide supports compliance with EU AI Act mandates, including likeness verification, private models, and continuous monitoring.
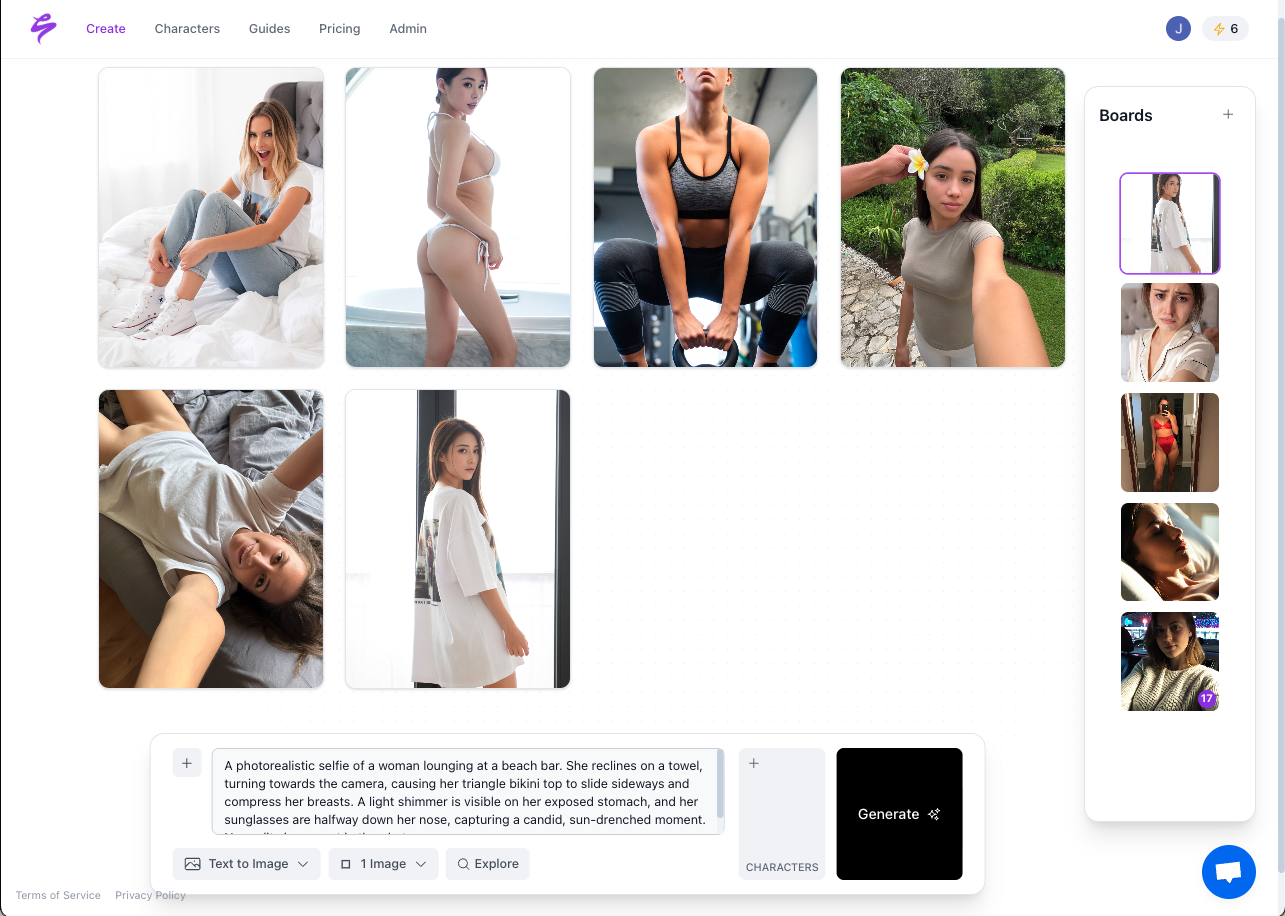
- Sozee.ai excels with 3-photo private likeness creation, agency approvals, and SFW-NSFW pipelines tailored to creator economies and regulatory compliance.
- Teams can implement these strategies securely by signing up with Sozee.ai for privacy-first, scalable content generation.
Digital Identity Risks in Text-to-Image AI Workflows
Enterprise digital identity traditionally rests on four pillars: possession (what you have), knowledge (what you know), inherence (what you are), and biometrics (biological markers). Modern IAM frameworks integrate these pillars with Zero Trust architectures, and text-to-image AI now adds likeness as an AI-based inherence factor that needs dedicated governance.
The threat landscape has intensified rapidly. Deepfakes account for 40% of all biometric fraud attempts, and fraud attempts using deepfakes increased by 2,137% over the last three years. The 2026 regulatory environment compounds these risks, with EU AI Act Article 50 requiring dual-layer labeling and C2PA metadata compliance by August 2026, carrying fines up to €15 million.
| Risk Category | Enterprise Impact | Text-to-Image AI Specifics |
|---|---|---|
| Brand Impersonation | $680K average loss | Unauthorized likeness theft in creator pipelines |
| Regulatory Non-Compliance | €15M potential fines | Missing C2PA watermarks, unlabeled synthetic content |
| Content Fraud | Reputation damage | Deepfake infiltration of marketing assets |
Five Enterprise Strategies for AI Identity Protection
Enterprise leaders use five focused strategies to protect digital identities inside text-to-image AI workflows.
1. IAM and RBAC Framework Integration
Enterprise governance in AI platforms for 2026 emphasizes RBAC, audit trails, and compliance logging as core features. Organizations define role-based permissions that control who can generate, approve, and distribute AI-created content.
2. Liveness Detection and Biometric Verification
Advanced liveness detection blocks synthetic identity injection during the initial likeness capture phase. Teams use real-time facial movement analysis and multi-factor biometric confirmation before model training starts.
3. C2PA Watermarking and Provenance Tracking
C2PA 2.0 introduces invisible watermarking embedded into image signals, surviving social media re-encoding, screenshots, and compression. This approach provides tamper-evident provenance even after metadata stripping.
4. Private Model Isolation
Enterprise-grade text-to-image platforms maintain isolated, private models for each authorized user. This structure prevents cross-contamination and blocks unauthorized access to proprietary likenesses.
5. Comprehensive Audit Trails and Oversight
Identity management frameworks must evolve for agentic AI. Enterprises now require detailed logging of generation requests, approvals, and content distribution.
| Strategy | Implementation Tool | Enterprise Benefit |
|---|---|---|
| C2PA Watermarking | SynthID, Adobe CAI | Survives metadata stripping, stronger fraud detection |
| RBAC Integration | Active Directory, Okta | Granular access control, automated compliance |
| Private Models | Enterprise platforms | No cross-contamination, IP protection |
Six-Step Playbook for Secure Text-to-Image Pipelines
Secure digital identity management in text-to-image AI follows a clear six-step playbook.
Step 1: Assess Organizational Needs
Teams review existing creator pipelines, content volume, and regulatory obligations. They map current IAM infrastructure and highlight integration points for AI workflows.
Step 2: Implement RBAC and Access Controls
Security leaders configure role-based permissions that define who can upload likenesses, generate content, approve outputs, and access private models. They integrate these controls with Active Directory or other identity providers.
Step 3: Deploy Liveness and Identity Verification
Organizations establish multi-factor verification for initial likeness capture. They combine real-time liveness detection, document verification, and biometric confirmation to block synthetic identity injection.
Step 4: Generate Content with Private Models
Teams use isolated, private text-to-image models that store individual likeness data without cross-user contamination. These models must support enterprise-grade security and compliance requirements.
Step 5: Apply Watermarking and Export Controls
Security teams implement C2PA-compliant watermarking for all generated content. They configure export controls that keep proper labeling and metadata intact across every distribution channel.
Step 6: Monitor and Audit Continuously
Organizations build logging and monitoring systems that track generation requests, content approvals, and distribution patterns. Organizations report 5x velocity improvements when they adopt mature AI governance frameworks.
Sozee.ai simplifies these steps with a three-photo upload system that creates instant private likenesses, built-in agency approval flows, and SFW-NSFW content pipelines tuned for creator monetization. Start creating now with Sozee.ai to scale content production while protecting privacy.
Why Sozee.ai Fits Modern Creator Economies
Sozee.ai focuses on the real needs of creator economies, including agencies and top creators. General identity verification platforms such as Jumio or Oracle center on authentication and access control, but they lack the specialized features required for scalable content generation.
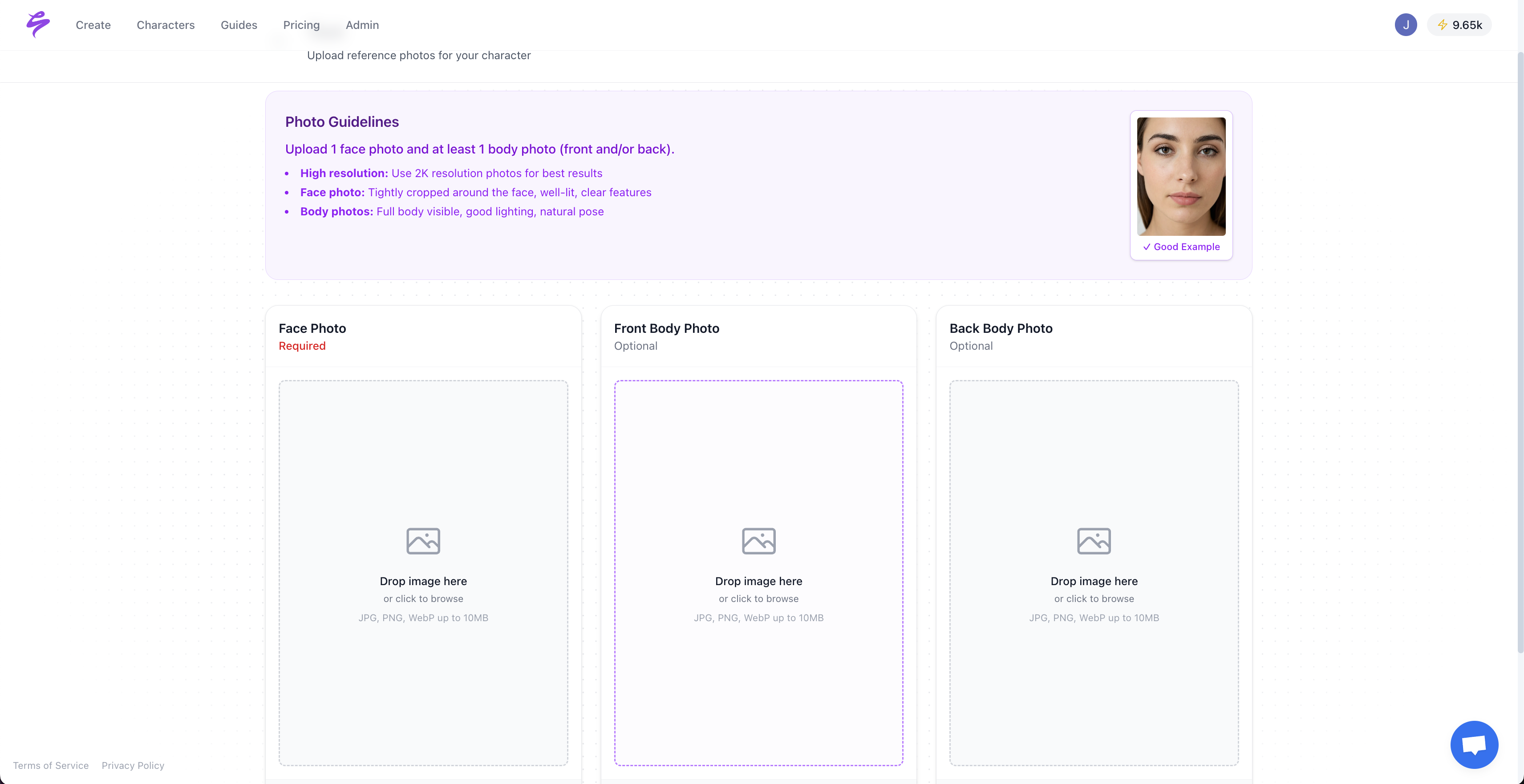
Sozee.ai stands out through minimal input requirements, since three photos create hyper-realistic private models without long training cycles. The platform maintains isolated private models for each user and prevents cross-contamination. Enterprise case studies demonstrate successful RBAC integration preventing unauthorized access to production systems.
The platform’s monetization-focused design includes prompt libraries, style bundles, and approval workflows tailored to agency operations. Content outputs reach a level of hyper-realism that passes human scrutiny while keeping brand consistency across campaigns.
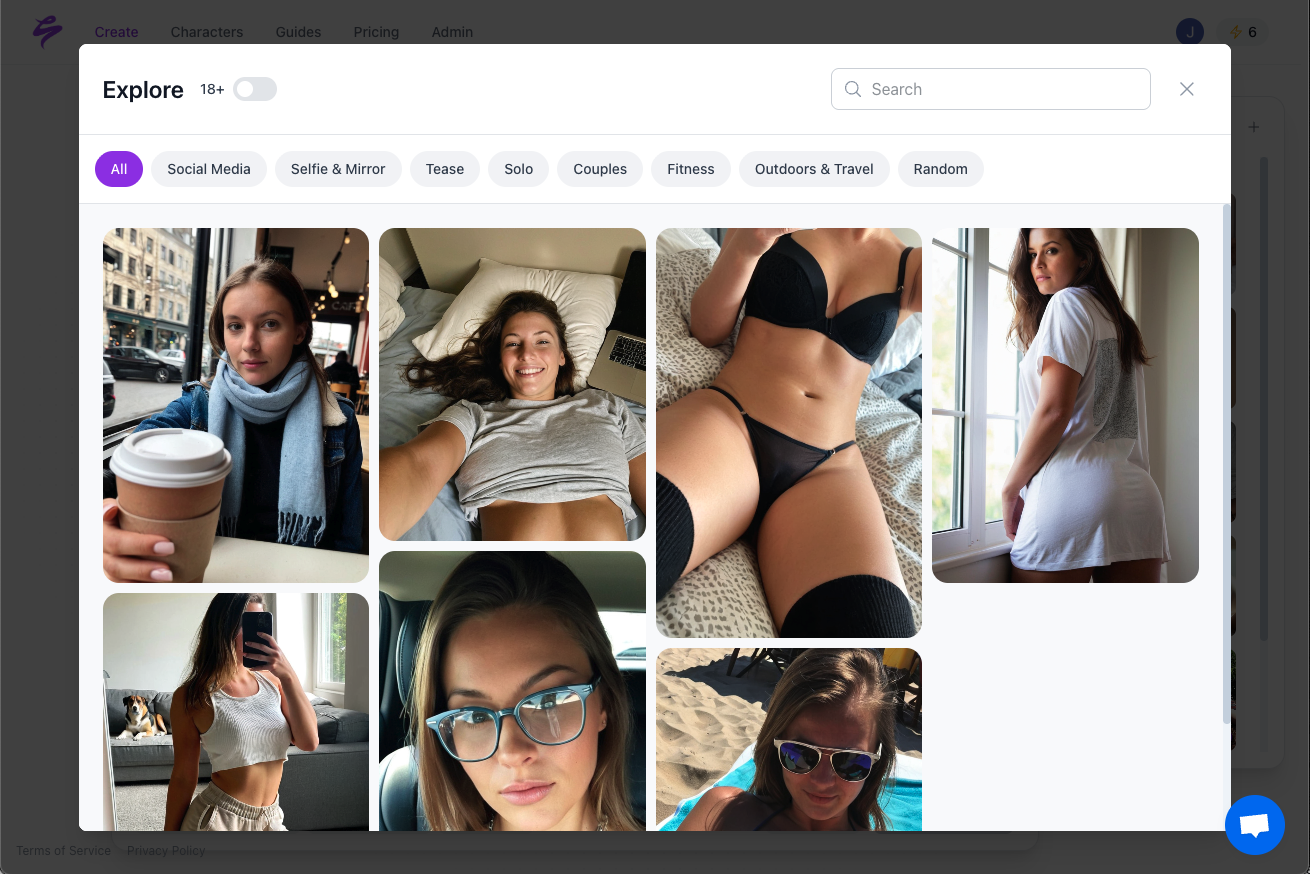
Agencies that manage multiple creators can scale content without causing creator burnout. Sozee.ai supports SFW-to-NSFW content pipelines, custom fan request fulfillment, and cross-platform optimization for OnlyFans, TikTok, Instagram, and other creator monetization channels.
Go viral today securely with Sozee.ai’s privacy-first approach to creator content generation.
Creator and Agency Challenges with Text-to-Image AI
Creator and agency teams encounter several recurring challenges when they adopt text-to-image AI workflows.
Inconsistent Output Quality: Generic AI platforms often deliver uneven results across prompts and styles. Sozee.ai counters this issue with private models and style consistency features tuned for creators.
Regulatory Concerns: Many platforms fail to label content correctly or preserve metadata. Sozee.ai focuses on privacy with isolated models that never train any other system.
Performance Metrics: Properly implemented AI governance frameworks deliver 50% fraud reduction and 5x operational velocity improvements.
| Challenge | Common Pitfall | Sozee Solution |
|---|---|---|
| Model Inconsistency | Generic training data | Creator-optimized private models |
| Privacy Gaps | Shared models | Isolated private likeness models |
| Access Control | Weak permissions | Agency approval workflows |
Future-Proofing Digital Identity in AI Content
Managing digital identities within text-to-image AI now requires frameworks that combine traditional IAM principles with specialized AI governance. The 2026 regulatory landscape demands fast action, and the creator economy’s growth requires flexible, scalable solutions.
Sozee.ai bridges enterprise security requirements and creator monetization workflows. By running secure, compliant text-to-image AI processes, organizations can scale content production while staying compliant and protecting their brands.
Get started with Sozee.ai to build compliant creator operations in a fast-changing digital landscape.
Frequently Asked Questions
How is AI used in identity verification for text-to-image generation?
AI identity verification in text-to-image contexts combines traditional liveness detection with specialized likeness authentication. The process uses real-time facial movement analysis during initial capture, biometric confirmation against government documents, and continuous monitoring for synthetic identity injection. Text-to-image AI verification also protects against unauthorized likeness recreation and ensures only verified individuals can create private models of their appearance.
What are the 4 pillars of digital identity in AI-generated content?
The four pillars of digital identity in AI contexts are possession (cryptographic keys and device certificates), knowledge (passwords and security questions), inherence (biometric data and behavioral patterns), and AI-specific likeness (verified facial and voice characteristics). In text-to-image AI, likeness effectively becomes a fifth pillar that needs protection through private model isolation, watermarking, and provenance tracking to prevent unauthorized recreation or deepfake attacks.
How do enterprises manage digital identity with text-to-image AI?
Enterprise digital identity management for text-to-image AI follows a six-step process. Teams assess organizational needs and compliance requirements, implement RBAC access controls integrated with existing IAM systems, deploy liveness detection and identity verification for initial likeness capture, generate content using private isolated models, apply C2PA watermarking and export controls, and maintain continuous monitoring with audit trails. This structure supports regulatory compliance and scalable content generation.
What are the main deepfake risks to digital identity in creator workflows?
Deepfake risks in creator workflows include unauthorized likeness theft that drives brand impersonation, synthetic identity injection during model training, content fraud through deepfake infiltration of marketing assets, and regulatory violations from unlabeled synthetic content. These risks have intensified as deepfake fraud attempts increased 2,137% over three years and average enterprise losses reached $680,000 per incident. Effective mitigation uses identity verification, private model isolation, and strong watermarking systems.
How does C2PA watermarking protect against deepfakes in enterprise AI workflows?
C2PA watermarking protects AI-generated content by embedding invisible, tamper-evident watermarks directly into image signals. These watermarks survive social media compression, screenshots, and format conversion, so authenticity checks still work after metadata stripping. The technology stores cryptographic hashes linked to manifest repositories, which allows detection algorithms to verify content origins and flag potential deepfakes. C2PA 2.0 soft bindings support enterprise IP protection and regulatory compliance under 2026 EU AI Act requirements.
